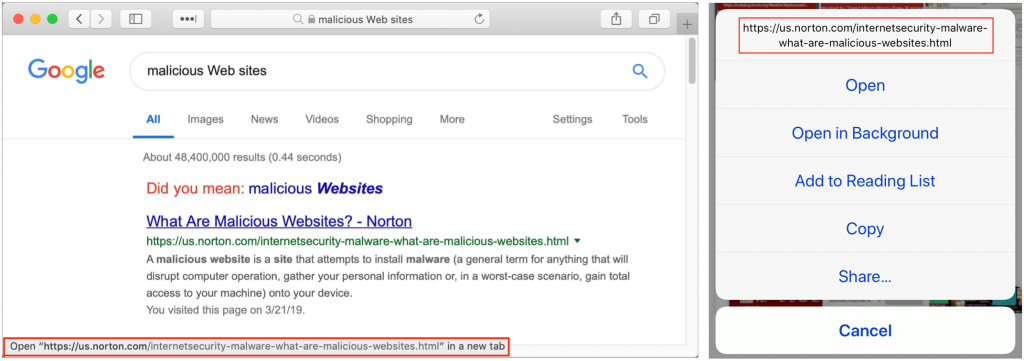
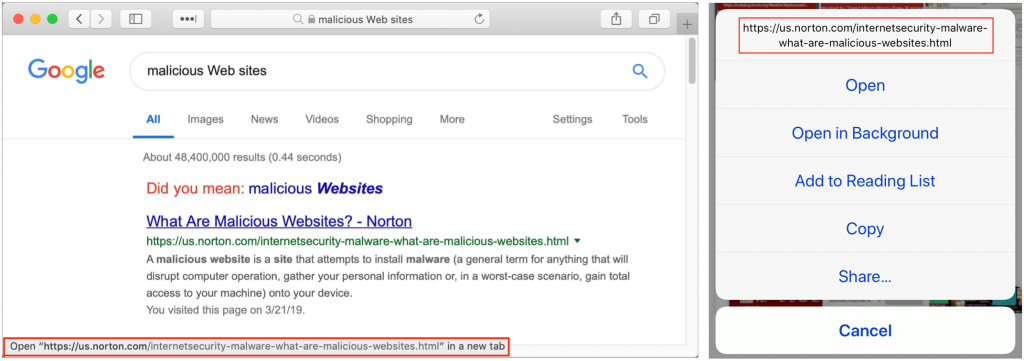
When you follow a link in Safari, you generally don’t know where you’re going to end up. That’s fine most of the time, but what if you’re concerned that a site might be trying to trick you into going somewhere malicious? Safari provides an easy way to look at the URL under a link. On the Mac, choose View > Show Status Bar, hover your pointer over the link, and look at the bottom of the window. In iOS, touch and hold a link (don’t press for 3D Touch) until a popover appears, showing the link and giving you options for opening it. The most important thing to look at is the domain—us.norton.com in the screenshots. It should match where you think you’re going, or at least look reasonable. If the URL is dubious, don’t follow the link.